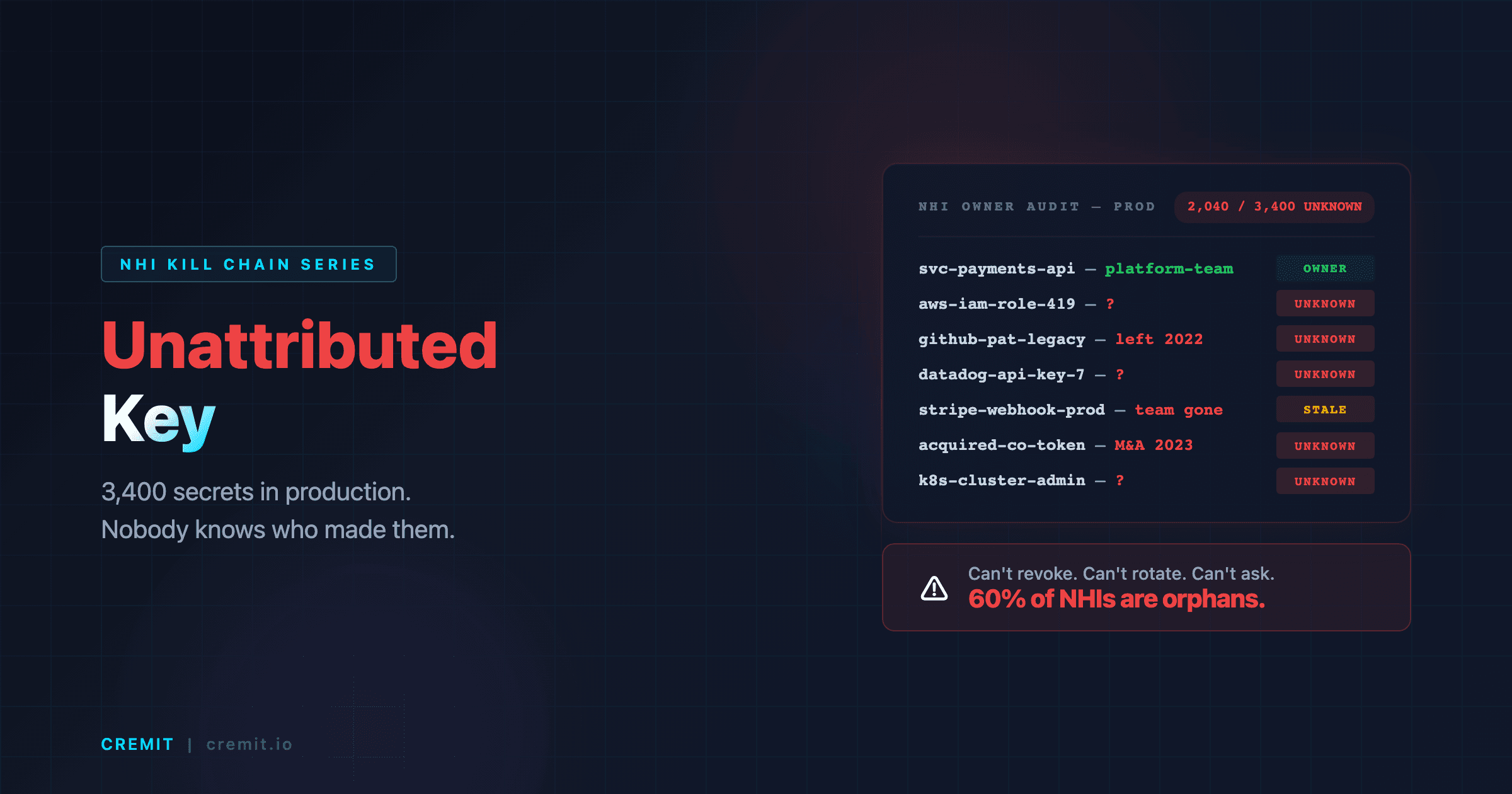
Ownerless API Keys: When 60% of Your Credentials Have No Identifiable Owner (NHI Kill Chain #8)
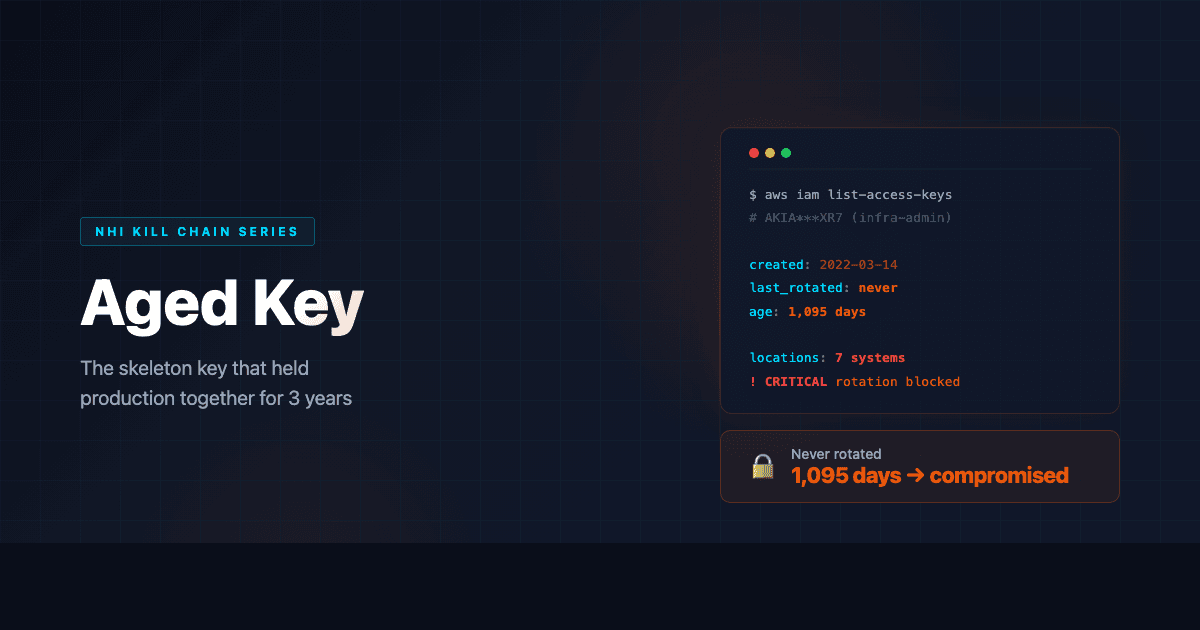
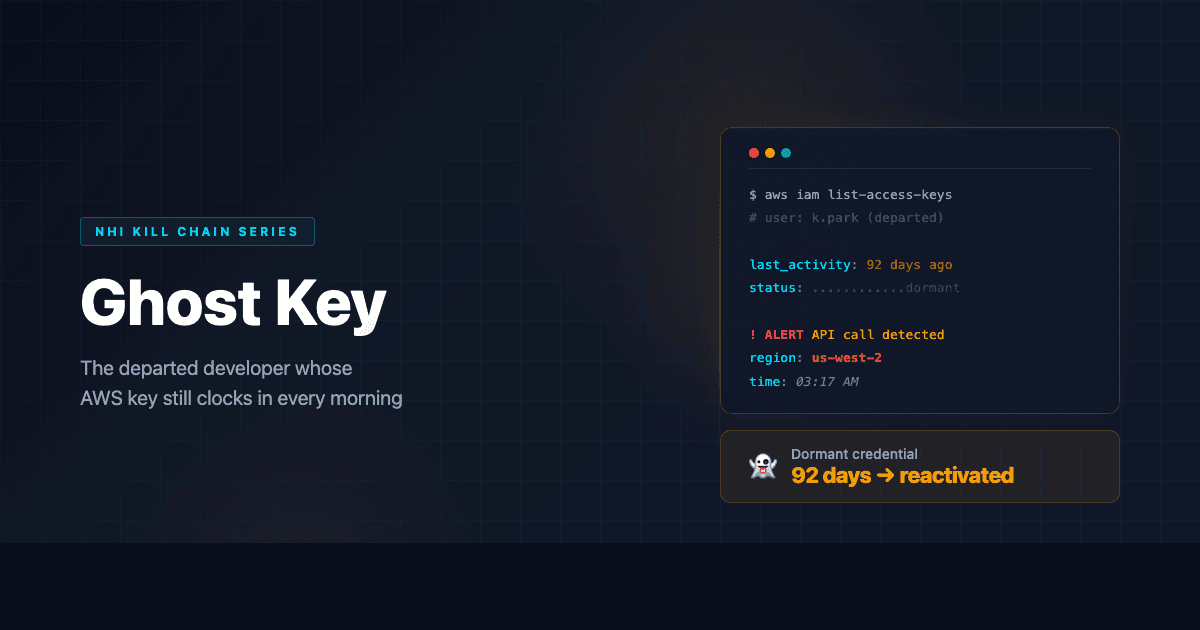
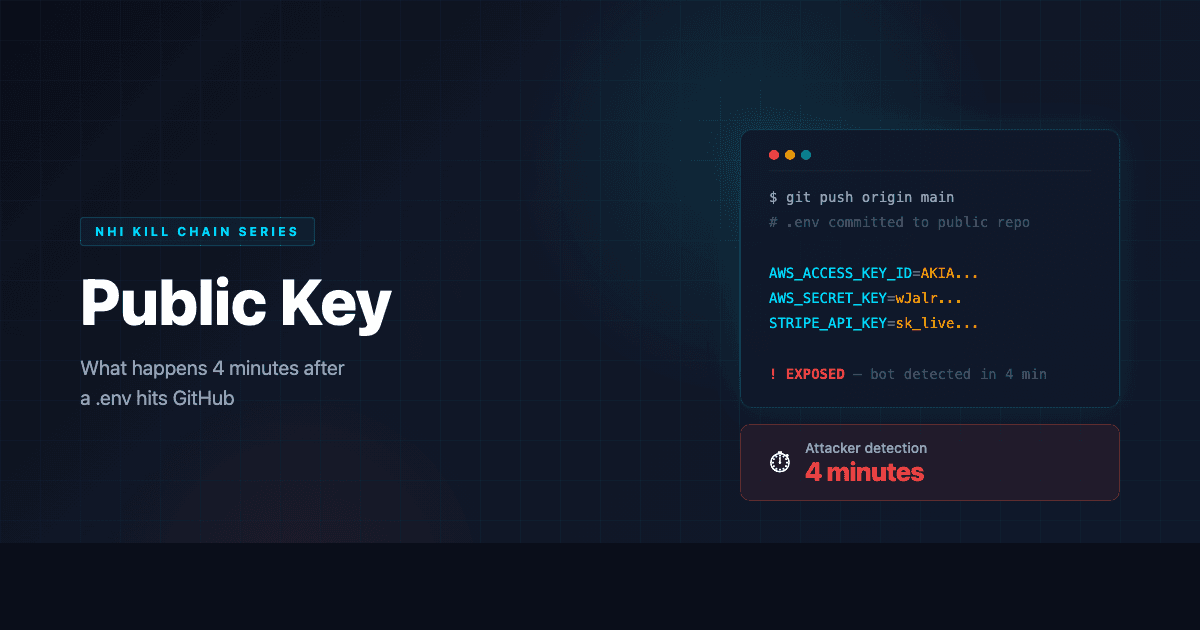
A new CISO ordered a full NHI audit. The result: 3,400 active credentials, 60% with no identifiable owner. Can't revoke them, can't rotate them, can't assign responsibility.