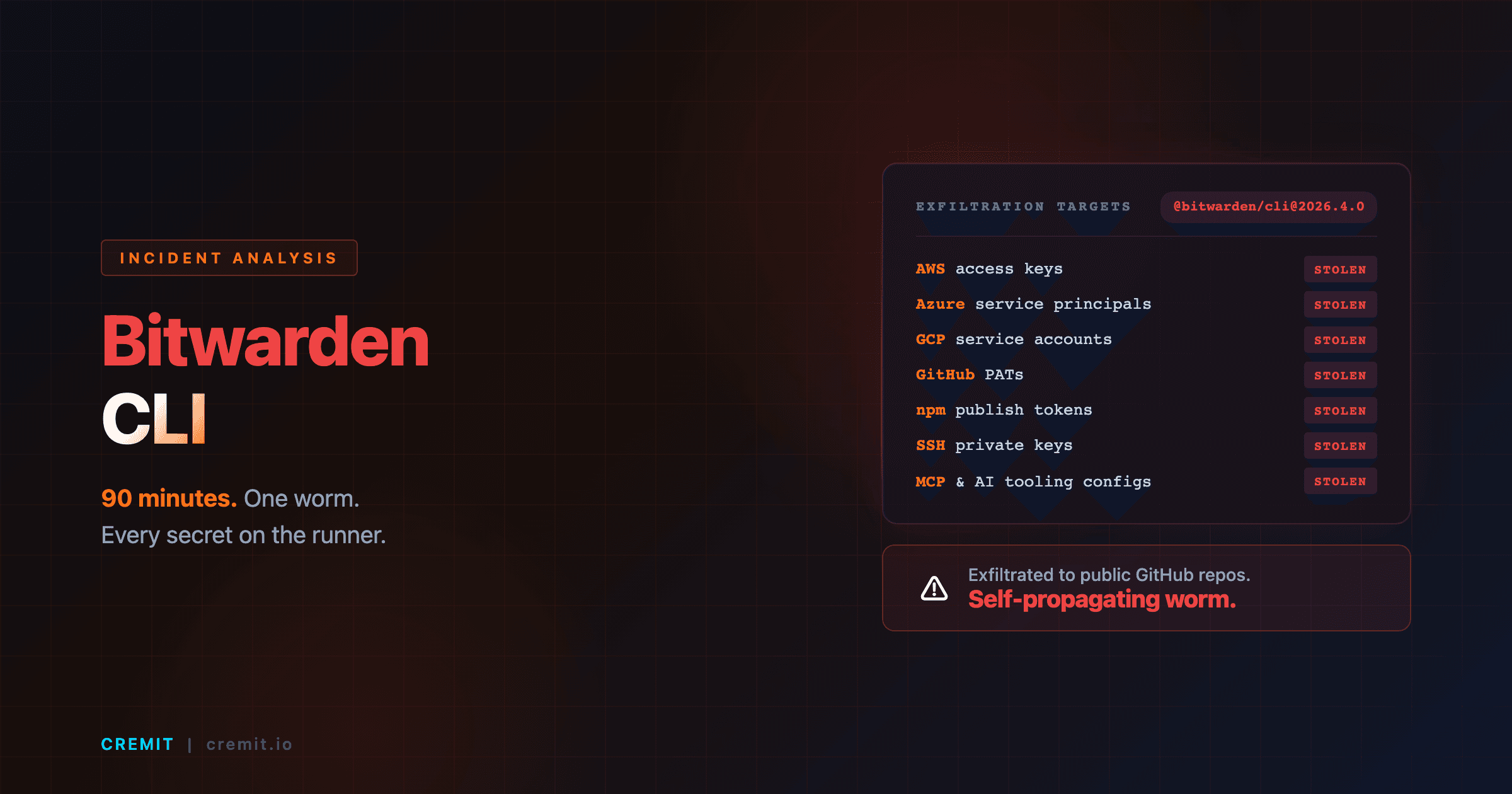
Bitwarden CLI Hack (April 2026): How a 90-Minute npm Window Stole AWS, GCP, GitHub Tokens
On April 22, 2026, the official @bitwarden/cli@2026.4.0 npm package was malicious for ~90 minutes. A self-propagating worm exfiltrated AWS, Azure, GCP, GitHub, npm, SSH, and AI tooling credentials from CI runners. Vaults stayed safe. CI tokens did not. Timeline, NHI kill-chain mapping, and a 10-minute checklist to know whether you were affected.