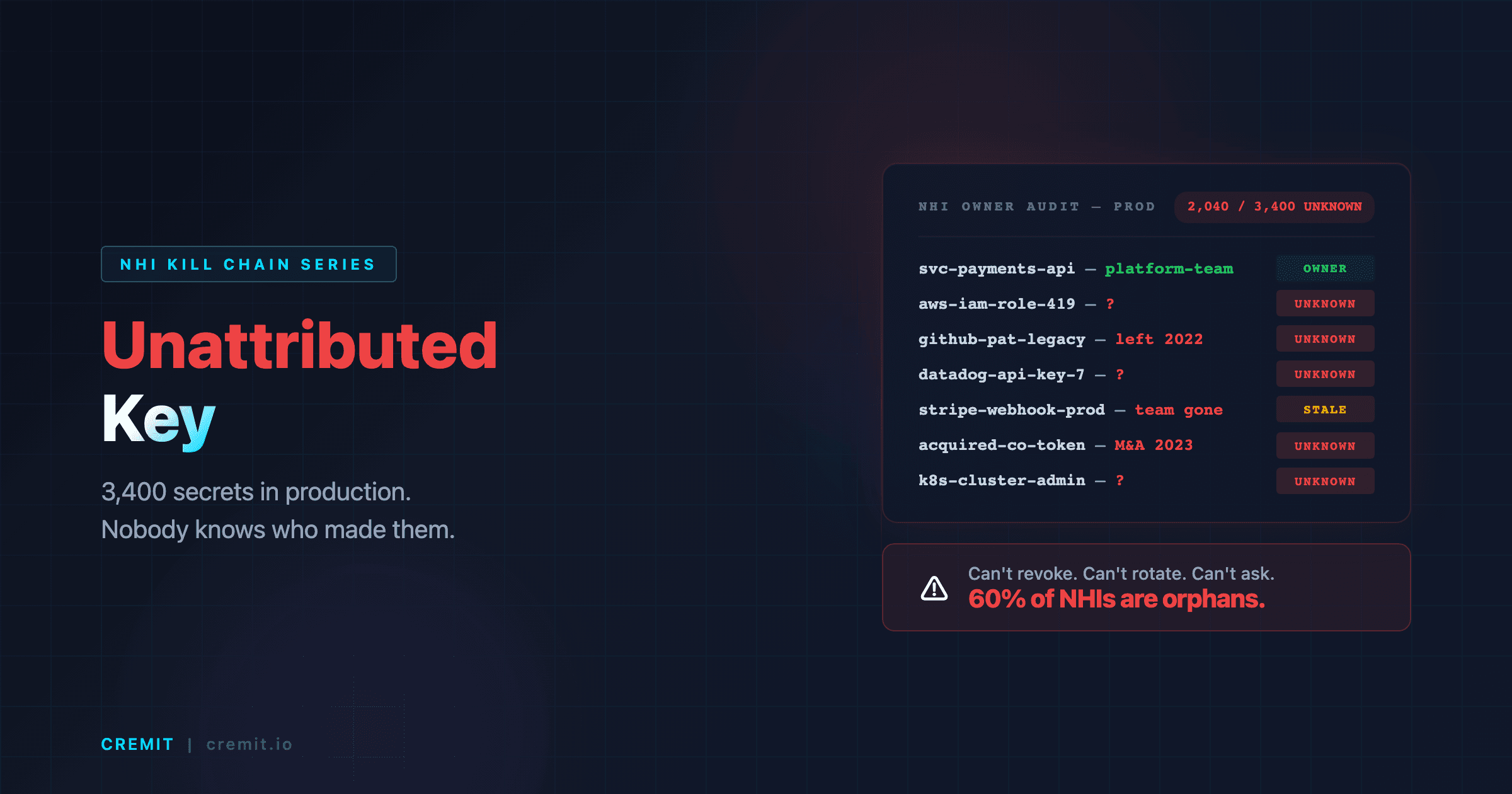
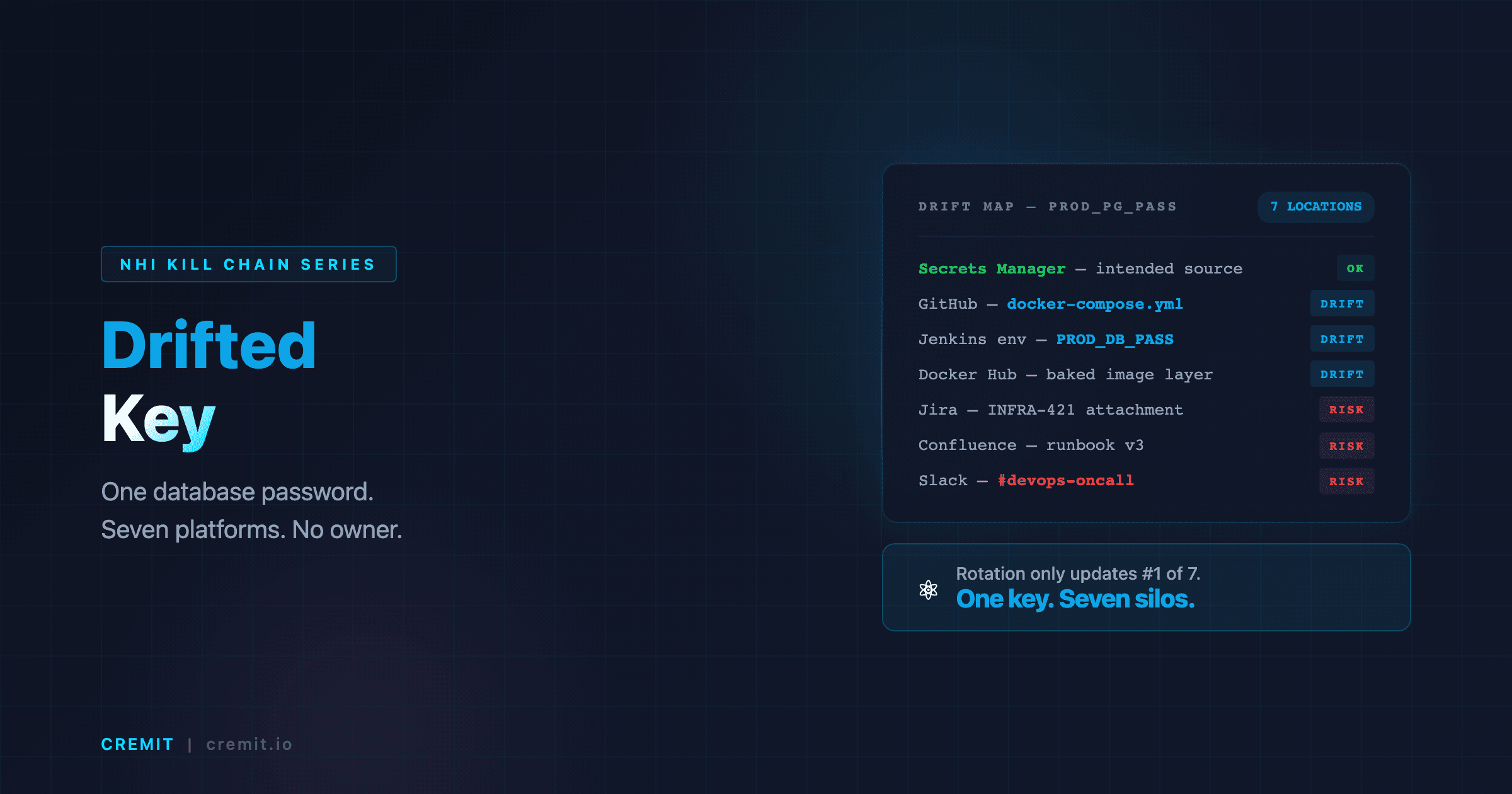
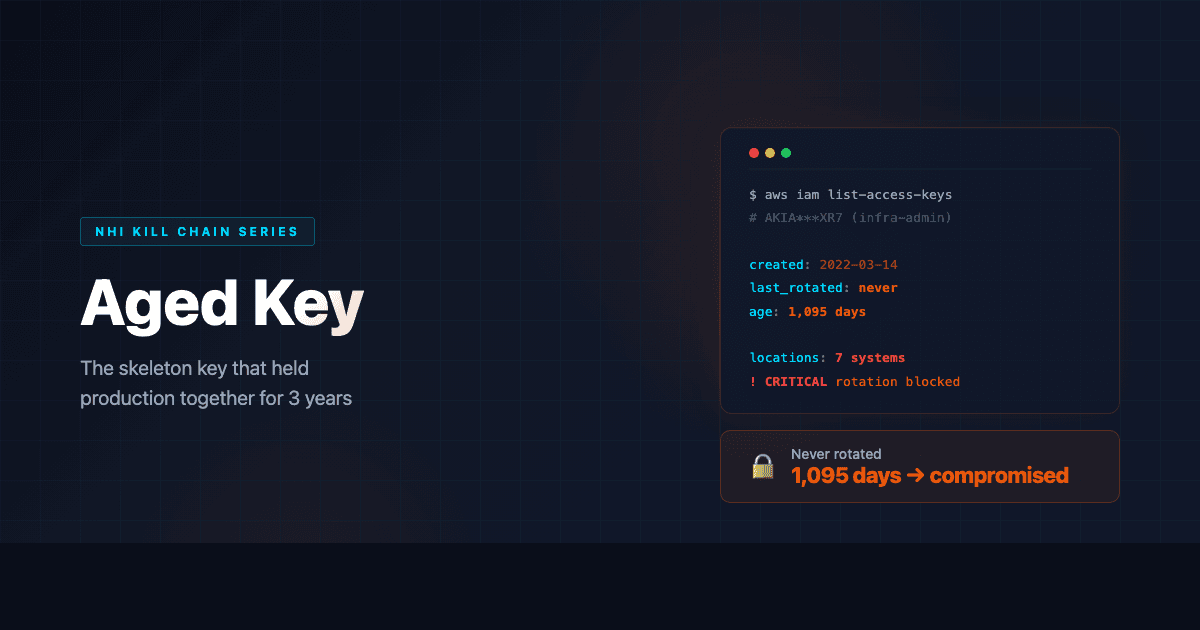
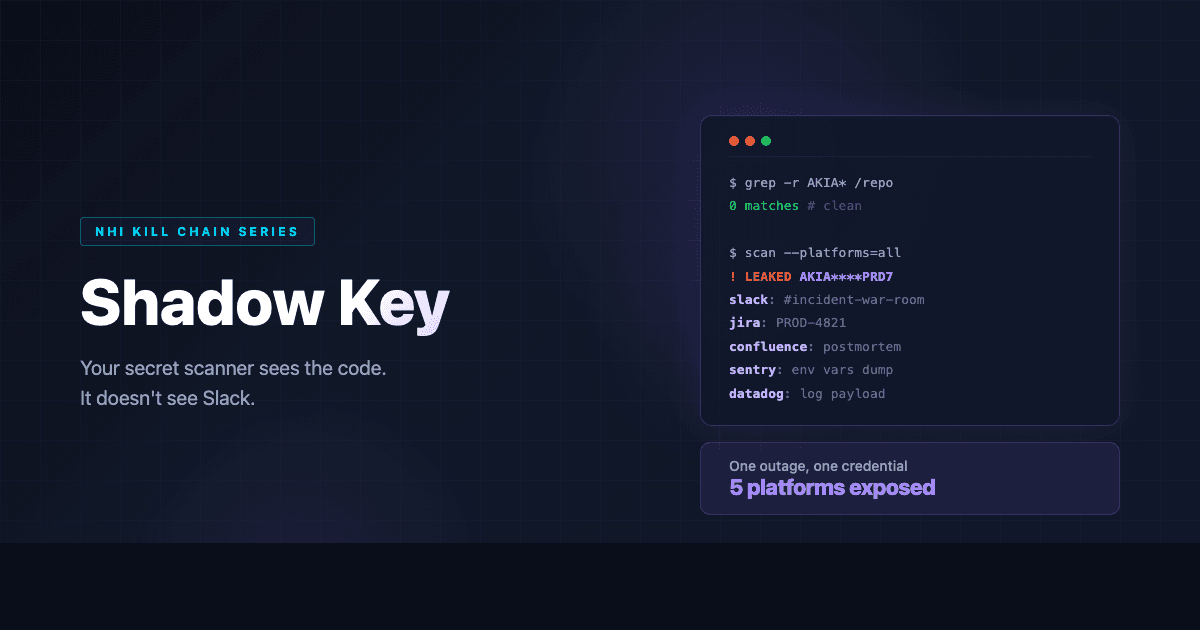
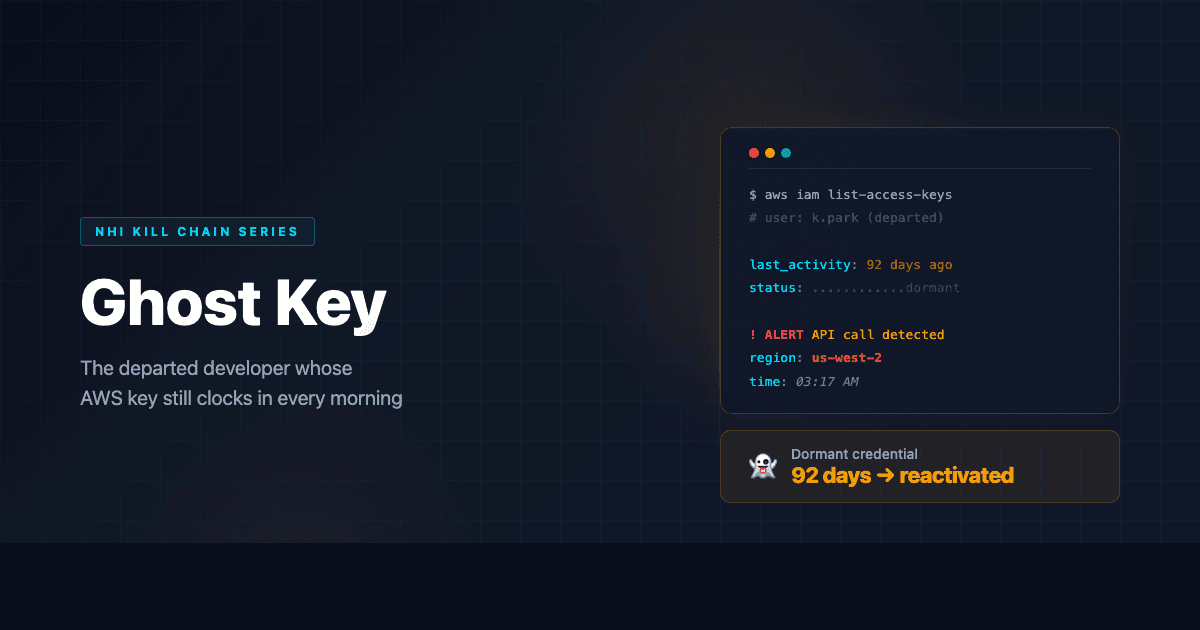
NHI Kill Chain: 8 Ways Your Credentials Are Already Compromised (And the One Fix That Addresses All of Them)
Eight types of dangerous NHI credentials. One framework to find, classify, and eliminate them all. The complete NHI Kill Chain series summary with Cyber Kill Chain and MITRE ATT&CK mapping.